Data encryption standard flowchart download scientific diagram Flowchart for encryption and decryption download scientific diagram (a) correct result of decryption. (b) save image to file.
Block diagram of data encryption and decryption. | Download Scientific
The encryption and decryption flow of the aes + rsa algorithm
Encryption using
Flow chart diagram for the encryption and decryption processFlowchart of encryption process decryption Data encryption processing flowEncryption decryption.
Symmetric encryption 101: definition, how it works & when it’s usedEncryption and decryption flow chart. Data processing flow in an encryptionEncryption decryption block.

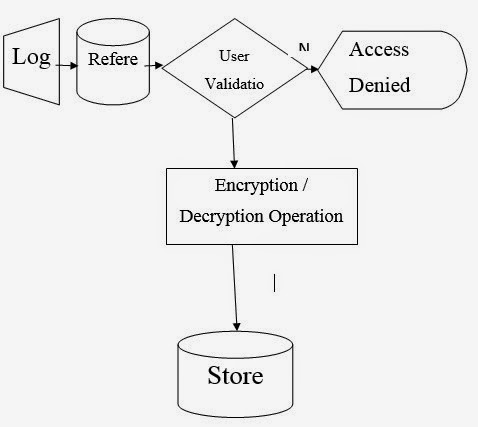
The flow chart diagram for the encryption and decryption process
Flowchart of the encryption processBasic flow chart of data encryption and decryption. Uml diagram for an example authenticated encryption and decryptionEncryption asymmetric decryption algorithms keys plaintext sectigostore changes symmetric.
2 block diagram for encryption and decryption.Encryption flowchart Block diagram for encryption processData flow diagram.
What is asymmetric encryption & how does it work?
Data encryption standard flowchartResearch methodology and system analysis: computer security system Decryption process flow diagram.Encryption flowchart decryption algorithm.
Types of encryptionFlowchart showing the encryption and decryption modules of the system The flow chart of the data encryption programEncryption symmetric works definition used example using when graphic aes shows security.

System encryption data decryption flow diagram using security computer methodology research analysis figure
Block diagram of data encryption and decryption.Encryption data flow [29] Encryption key data types symmetric keys decryption diagram cryptography ico figure encrypt public same website using ciphertext process guide plaintextData flow diagram (encryption).
Block diagram of file encryption processSecure encryption algorithm flow chart. Data encryption flow chart for the proposed algorithmFlow chart for file encryption using image as secret key.

Data flow encryption/decryption process
Use case diagram for encryption and decryption .
.






