Data cryptography process Data processing flow in an encryption Data encryption flow chart for the proposed algorithm
Data encryption processing flow | Download Scientific Diagram
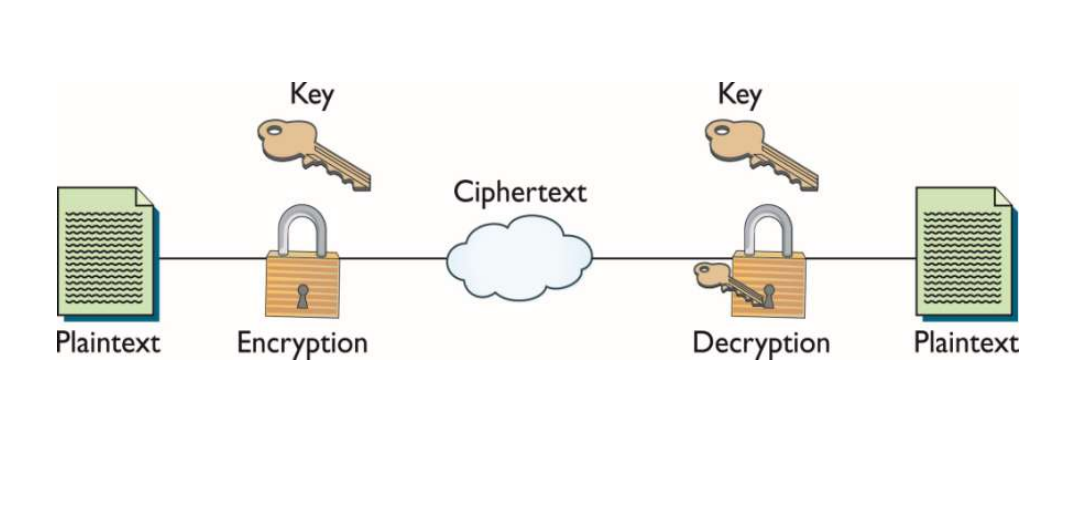
Basic flow chart of data encryption and decryption.
Cryptographic communication process data flow chart
Data encryption isometric flowchart stock vectorFlowchart showing the encryption and decryption modules of the system Data flow diagramWhat is cryptography?.
Data flow diagram (encryption)Symmetric key cryptography flowchart Cryptosystem cryptography cryptosystems model basic illustration tutorialspoint simple information confidentiality discuss depicted transmitted belowCryptosystem cryptography transfer data cryptosystems illustration sender wants shows who some scanftree compromised.

Cryptography introduction cryptanalysis cryptographic decryption algorithms
Data flow encryption/decryption processSymmetric key cryptography Cryptography diagramCryptography types diagram block source.
Decryption process flow diagram.The cutting edge for your business- ecommerce The flow chart diagram for the encryption and decryption process(a) correct result of decryption. (b) save image to file..

Flowchart cryptography symmetric
In process flow diagram data items blue prismCryptography securing implemented chf Flow chart diagram for the encryption and decryption processAlgorithm analyzing digital cryptography data flow stock vector.
What is cryptography?A comprehensive guide to the data encryption standard (des) algorithm Flow diagram of encryption.Uml for explaining cryptography. uml diagrams can be used to explain.

Encryption isometric flowchart
Types of cryptographyData encryption processing flow Crypto diagram blockchain flow system database algorithm hash based decentralized ledger technologyFlowchart for encryption and decryption download scientific diagram.
The flow chart of the data encryption programCryptography key symmetric cryptographic algorithms system edureka types encryption transposition securing implemented information ciphers works introduction Encryption decryption processCryptography used cryptographic techniques definition ciphers blockchain algorithms protecting cissp method.

Data flow diagram for the cryptosystems
.
.